How to Download TLS Certificates¶
Description¶
For proper operation of both the TLS server and TLS client authentication, the ATWINC1500B device must have a certificate/private key pair assigned to it.
An 8KB flash area is reserved for storing the TLS certificates starting from offset 20KB in the ATWINC1500B stacked flash.
The TLS certificates can be downloaded into the ATWINC1500B stacked flash by using the dedicated tool tls_cert_flash_tool.exe.
Tip
Before you start download, see Prepare for Setup for prerequisites.
Steps¶
Perform the following steps to download the custom TLS certificates:
-
Program Pitaya Go with the serial bridge firmware: serial_bridge_usb_pitaya_go_vx.x.x.hex.
-
Connect Pitaya Go to a Windows computer. Check the comport number of the device detected.
-
Generate the custom certificate/private key pair. See How to Create Custom TLS Certificates for more details.
-
Open CMD and navigate to the directory with tls_cert_flash_tool.exe:
cd .\pitaya-go\utils\wifi\Tools\tls_cert_flash_tool\Debug_UART\
-
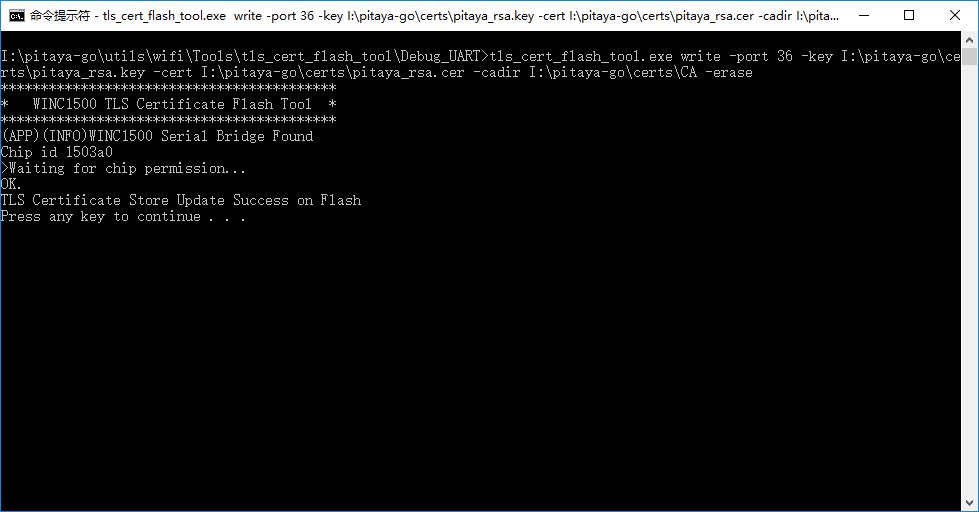
Run the following scripts to download the certificates:
If an ECDSA certificate is available, go on to run:tls_cert_flash_tool.exe write -port {comport} -key {private_key_path} -cert {rsa_cert_path} -cadir {ca_directory} -erase
The parameters stand for the following:tls_cert_flash_tool.exe write -port {comport} -nokey -cert {ecsda_cert_path} -cadir {ca_directory}
{comport}: Number of the serialport (e.g.36representsCOM36).{private_key_path}: Path of the TLS Private Key.{rsa_cert_path}: Path of RSA based Certificate.{ecdsa_cert_path}: Path of ECC based Certificate.{ca_directory}: A directory containing intermediate CA certificates and/or the Root CA certificate of the ATWINC1500B certificate chain(s).
-
After a few seconds, the following message appears to indicate that the root certificates are successfully downloaded.
Create an Issue¶
Interested in contributing to this project? Want to report a bug? Feel free to click here: